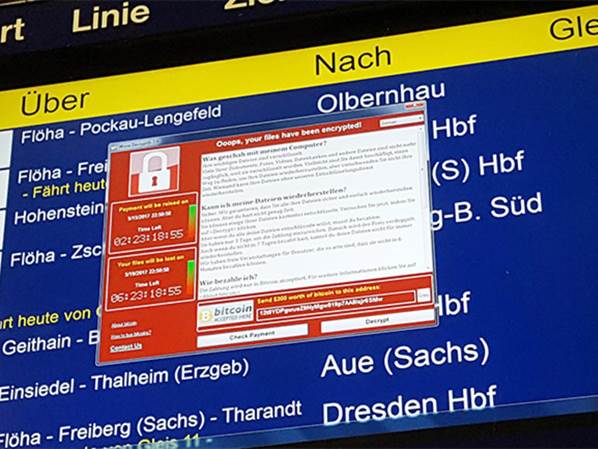
DSN: Ransomware News - WannaCry Ransomware
Windows users are still recovering from WannaCry ransomeware which first appeared on Friday May 12, 2017 and has leveraged stolen NSA hacking tools (dubbed “EternalBlue”) to perpetuate one of the largest ransomware attacks to-date, affecting more than 300,000 people in some 150 countries. The Ransomware is introduced to a computer using the typical phishing attempt to trick users into opening an attachment or visiting an infected website. The ransom demanded was typically $300 per infected computer. The NSA has released a statement that gives “moderate confidence” of attributing the creation of WannaCry to the North Korean government.
Primary victims have been those running unpatched Windows 7 or older, unsupported and/or unpatched version of Windows such as Windows XP and Windows Server 2003. Microsoft has recently released emergency patches for these older operating systems so if you haven’t already ran Windows update, it is strongly recommended that you run Windows update as soon as possible.
To help protect yourself and your organization from Ransomware, it is critical that you educate your users to avoid opening any email attachment that was not expected, deploy strong antivirus and antimalware software, keep PC and server patches up-to-date, and backup all data.